Yubikey - simple approach to authentication tokens

 Simon Josefsson was giving a talk on OpenID in the Scandinavian Free Software Conference. OpenID is a lightweight single sign-on and auto-registration system for web applications. In concept it is quite similar to Shibboleth but easier to deploy.
Simon Josefsson was giving a talk on OpenID in the Scandinavian Free Software Conference. OpenID is a lightweight single sign-on and auto-registration system for web applications. In concept it is quite similar to Shibboleth but easier to deploy.
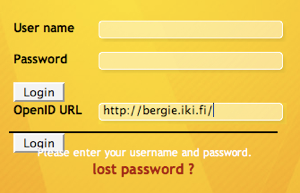
Since OpenID can solve a lot of issues with registration to social web services, Midgard has been supporting it since last August. However, OpenID has one major security problem: as the cross-site redirections are controlled by the site user is visiting, OpenID has quite a high potential for phishing attacks. One way to reduce that risk is to use one-time passwords with OpenID instead of the usual username/passphrase combination.
Enter Yubikey
The problem with OTP is that disposable password lists are a lot of hassle. RSA’s SecurID device has been one approach to solve that by having a simple device to generate the one-time passwords that user can then enter on their computer. But SecurIDs are expensive and manually typing the number sets is tedious.
Simon’s company Yubico has approached the problem from a bit different direction: their Yubikey is a small, cheap USB dongle that the computer sees as a “keyboard”. Insert the key, press the button, and the one-time password will be entered.
I was given a key and have been testing it a bit today to authenticate via my OpenID identity to various websites, and it really was as easy as advertised. Now my OpenID is secure.
 In addition to OpenID, Yubikey authentication is supported via RADIUS and PAM, and libraries are available for integrating it with other authentication systems.
In addition to OpenID, Yubikey authentication is supported via RADIUS and PAM, and libraries are available for integrating it with other authentication systems.
Yubikey is not without problems, unfortunately. While authentication client libraries are open source, the actual authentication server is proprietary and operated by Yubico, a small start-up. If Yubico’s network goes down, the whole authentication system becomes unusable.
I’d love to use Yubikeys for my company and several of my customers. Therefore, I really hope Yubico will be able to either release the server sources directly, or at least make a pledge to release them in case of going out of business. Only these options would make Yubikey a really viable secure authentication option.
Technorati Tags: authentication, openid, securid, yubikey